Making Safe (and Memorable!) Passwords
Posted by Aitan on 2017 Feb 21st
There's a subtle moment of panic and bewilderment on people's faces when I ask what their computer password is. Sometimes it'll roll off the tongue, but all too often an fearful expression descends, as though the police were demanding your driver's license.
Passwords can reduce even a proficient user to the level of a novice. Know this though — if this is you, you are in the company of giants. No one can call themselves a password master. Everyone struggles to manage them.
Password management methods range from scraps of paper to detailed notebooks and specialized "master password" applications. Written down, synced across your devices, or all up in your head, we're all swimming in a soup of letters and numbers. I'd like to help you feel a little easier about the whole mess.
What makes a good password?
You and I both know that 15 years ago all we had to do was use a word like “apple” – so that’s exactly what we did. Then someone came along and said “Hey, we can crack that in less than a day…” (computers were slower then), “…you must use a number.”
apple1
"You must use a capital…”
Apple1
“You must use 8 characters…”
Apple123
“You must use a symbol…”
Apple123!
Nowadays, every account you create will have slightly different security requirements, but there are a few core elements that will satisfy 95% of all web services:
- Must be 8-12 characters in length
- Must have at least one capital letter
- Must have at least one lowercase
- Must have at least one numeral
The other 5% will ask you for symbols.
Now we’re getting somewhere — Create a system to either store or remember your passwords
At the end of the day, this is about security. The biggest advice I can give you is to have some kind of a system—any kind of system—and recognize which ones are most secure. But regardless of what that system is, the best way of keeping it up to date is to write the password down first, before you register it.
Basic methods of storing passwords, in ascending order from sketchy to safe:
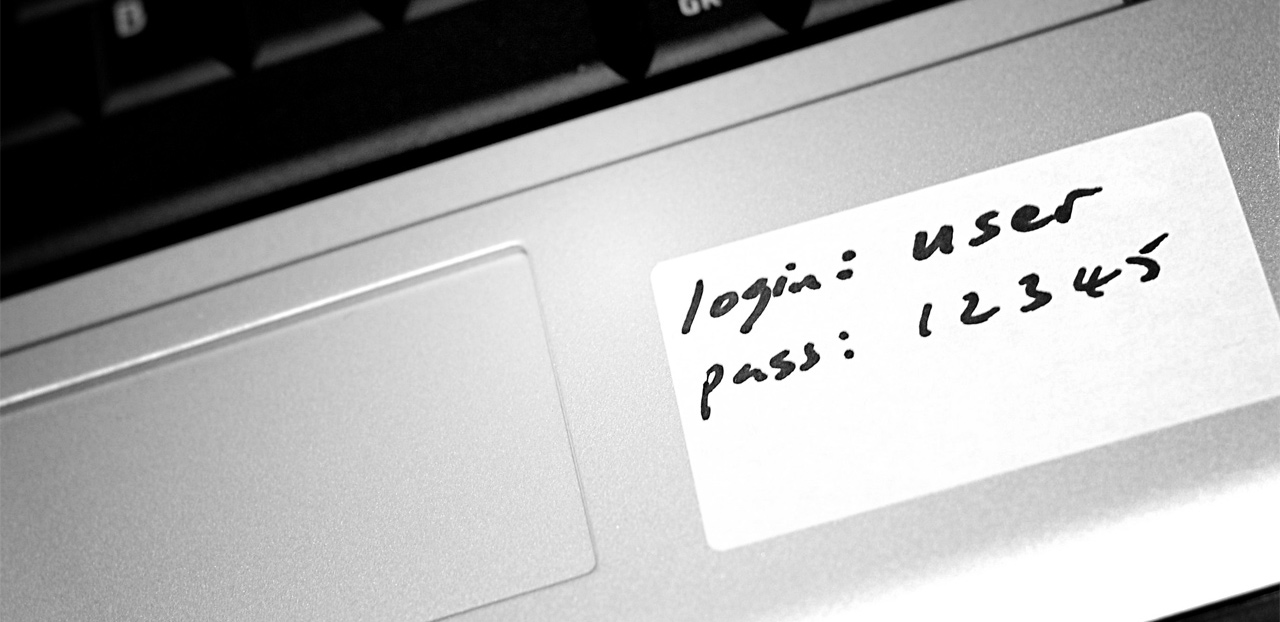
- Random / doodlesque passwords on a sheet of paper under the keyboard or in a folder — this doesn’t work and dooms you to a lifetime of frustration, chaos, and disaster if someone nabs it.
- The Word Document — Only a stone's throw away from the previous method. While easy to use, it can be easily accidentally deleted, easily copied or stolen, doesn’t have any meaningful security, and most of all tends to get lost in disorganized document folders, so you default back to the safety net of a printed copy.
- The iCloud address book as a password store — this is a surprisingly common method of storing passwords, but in addition to the fact the the passwords are often visible (as opposed to “obfuscated” with little dots) many people also have unresolved iCloud sync problems across their devices, leading to obsolete passwords littering their address book.
- The little black book — Believe it or not, this is actually my best recommendation if you’re intimidated by software-based password systems. It’s a logical and well used human construct that people are used to maintaining, and has the benefit of being able to be hidden in a safe location along with the remainder of your valuables. Do this over any of the above methods.
Time to get serious.
All of the following, more advanced methods have one basic principal at their core: you must have a unique, hard to guess password to get into your computer. It doesn’t have to be a Fort Knox password, just something memorable that few others know. Better yet, use FileVault to encrypt your drive. Then no-one is getting at the data inside.
- Various third-party password management apps — there are lots of nicely curated applications available in the App Store that allow you to store your passwords in an encrypted form (scrambled without a password to get in). Many allow you to sync across your devices, but they are also not as heavily vetted as the others on this list. Additionally, many also utilize access and syncing through their own websites, which leave them vulnerable to targeted hacks and breaches.
- Apple Keychain — excellent, safe, trustworthy method of saving passwords to websites, email, servers, anything. Just don’t have a password like “apple”, “password" or no password at all to get into your computer. I always get asked, “Should I allow Safari to save my passwords?” My answer is always “Leave out your banking passwords if you wish, but as long as your computer has a decent password, go for it with gusto."
- 1Password by Agilebits — the de facto standard in password management, this software—while pricey—has received the most attention and scrutiny and has stood the test of time. The database technology is fully encrypted, and uses fully encrypted sync technologies like iCloud and Dropbox to allow you multi-device access. Many iOS app developers have also built hooks into their software that allow you to access the database to log into their systems.
Memorable vs. Random?
If you use a password manager, you the have the option to use passwords that are very unlikely to be cracked, like a 16 or more random character password with symbols:
dGW=[*LopFv[X4q6u4MrJa[fQx2u3RJ@ndYQ
However, most of us don’t want to do this, and even though these password managers do all the filling in for you, you will need to use a “Memorable” password in places that you often have to do the typing. Some examples of these are:
- iCloud / Apple ID — let’s face it, you’re always being asked for this, and if you lose your iPhone, you’re going to need to log onto iCloud.com and find it.
- gmail.com / webmail — getting into your email at an internet café or abroad may be necessary in an emergency
- Banking — since this might not be among your saved passwords, it needs to be memorable and easy to use.
Memorable passwords are often practiced passwords.
Welcome to the Password Recipe
A password recipe is a simple, repeatable set of ingredients to make a useful password. For example, at its most basic:
[Family Member Name][Year][Symbol] e.g. Thomas2014$ or Lassie2017%
Now, in cases other than most at-home consumer computers, these are totally unsuitable.
Why? Because a home computer is neither a target for, nor susceptible to repeated breach attempts. No-one is going to sit at your computer at home and try to manually guess your password, or apply sophisticated methods to break in.
Websites, online services and corporate computers are a totally different situation however.
Websites and online services are under a constant onslaught of motivated and well-equipped attacks by potentially thousands of computers (botnets), because the payoffs here are significant.
Therefore, using what are referred to as "common name" or "dictionary terms” in a password recipe is inadvisable, as these are very easily broken in a targeted breach attempt.

Making a better Password Recipe
A more board-spectrum password recipe is a formula for creating memorable passwords for the dozens or hundreds of online services that we use. It has elements that relate to the service (like eBay or Apple) without actually using the word. It is also made up of (seemingly) random characters, and satisfies the common requirements for a modern password.
Some examples of good recipes (none of these are recipes that I or anyone else I know use—I’m just making them up)
- 22-8[2nd & 3rd letter of domain name]$[Last 2 letters of Son’s middle name (last capitalized)] for example:
- 22-8pp$cK (for apple.com)
- 22-8oo$cK (for google.com)
- [Number of letters in domain root]@[1st & last letter of domain][Year you graduated]-[Letters after your name]
- 3@ae1978PhD (for apple.com)
- 2@ey1978PhD (for Ebay.ca)
You can truly make up whatever you want. Just stay consistent and record them and the recipe somewhere safe.
Additionally, you may want to factor in a revision code like A, B, or C, that you can easily go through, if you’ve had to change a password and it won’t let you use the same one. This could be added at the end or at a set point in the middle.
In conclusion
There are many strategies for managing passwords. I haven’t told you all of my secrets, but regardless of what method you arrive at, please be consistent and plan for the times when you need to change them.
If there’s one key tip that I would most impress upon you a second time?
Always write down your password first!
